DDoS Attack Free Essays - PhDessay.com.
Cybercrime is a burgeoning epidemic in modern crime. Criminals are increasingly attacking the foundation of the Internet to execute criminal activities, regardless of nationality or stature, inflicting serious harm and posing very real threats to victims worldwide as this sample essay will address. DDoS: Unmasking the Ku Klux Klan.
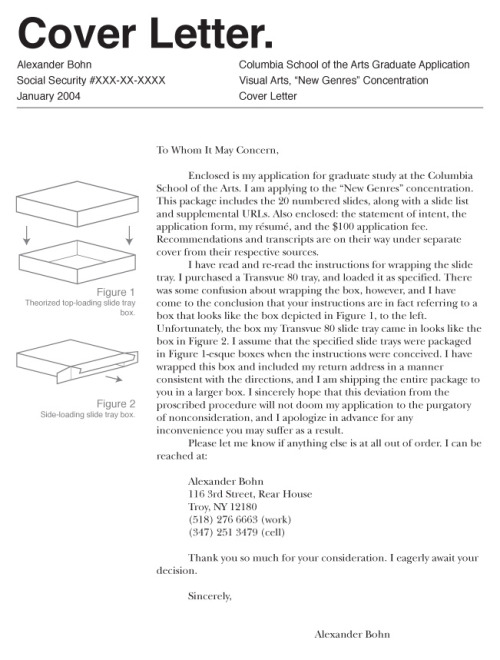
Denial of Service (DoS) attacks may become a major threat to current computer networks. Even a teenager can lunch the DoS attack by using readymade DoS tools. DoS attack is an attack to slow down the legitimate user’s computer by overloading its resources. The goal of DoS attack is to prevent the legitimate users to access the services, not.
Essay The Background Of Denial Of Service. Introduction Incentives for beginning a Distributed denial of service attack can be accidental, criminal extortion attempt, vandalism, financial market exploitation, etc., however, they are normally carried out to disturb daily operations and to extract funds.
The paper focus on the Interest flooding attack which is one the different type of Distributed Denial of service attack (DDOS).NDN incorporates better security features that detect and mitigate certain attack in the networks. But its resilience to the attacks has not analyzed yet. It presents the Distributed Denial of Service (DDOS) in Named.
An Anomaly Detection System For Ddos Attack Information Technology Essay. Evolving computing networks are fully dependent on cloud computing that provides reliable access across the various distributed resources. It has brought dramatic changes in the field of IT that significantly marks the various advantages such as providing services with.
Other posts on the site.
DDoS attacks involve the attacker sending high amounts of traffic at a precise target from different sources. The objective of the attack is to consume the supply of the target, so it is not capable of completing its normal functions or serve its user. The attack may try to overpower the target’s bandwidth, CPU or memory to render it useless.
Rlot Task 2 Essay 1004 words - 5 pages RLOT Task 2 With the availability of open source tools and resources to cybercriminals, it has become extremely difficult to combat distributed denial of service (DDoS) attacks. Typically DDoS attacks occur at the network layer by SYN flooding, ICMP flooding, and UDP flooding. Some times DDoS attacks fail.
Distributed denial-of-service attacks (DDos) DDoS refers to the type of attack that involves all computers within a network from any part of the world. In other words, unlike DoS which only involves one computer, the DDoS attack involves a lot of computers. This means that an attack on a single computer will eventually affect all the others in.
And with these parameters and many more also we build secure IDS to detect this kind of attack and block it. In this paper we discussed some attacks on MANET and DDOS also and provide the security against the DDOS attack. In existing system, Mobile ad-hoc networks devices or nodes or terminals with a capability of wireless communications and.